RSUSR200
Data Description
The RSUSR200 event is used in SAP to view the list of users by log-in date and password change information.
Potential Use Cases
This event could be used for the following scenarios:
Determine if there is abnormal log-in activity in the system.
Correlate the log-in data with other SAP Security system data to identify potential security threats.
Visualize inactive users in the system.
Understand if someone is attempting do a brute force log-in.
Identify which users need to change their passwords based on password aging.
Splunk Event
The event will look like this in Splunk:

SAP Navigation
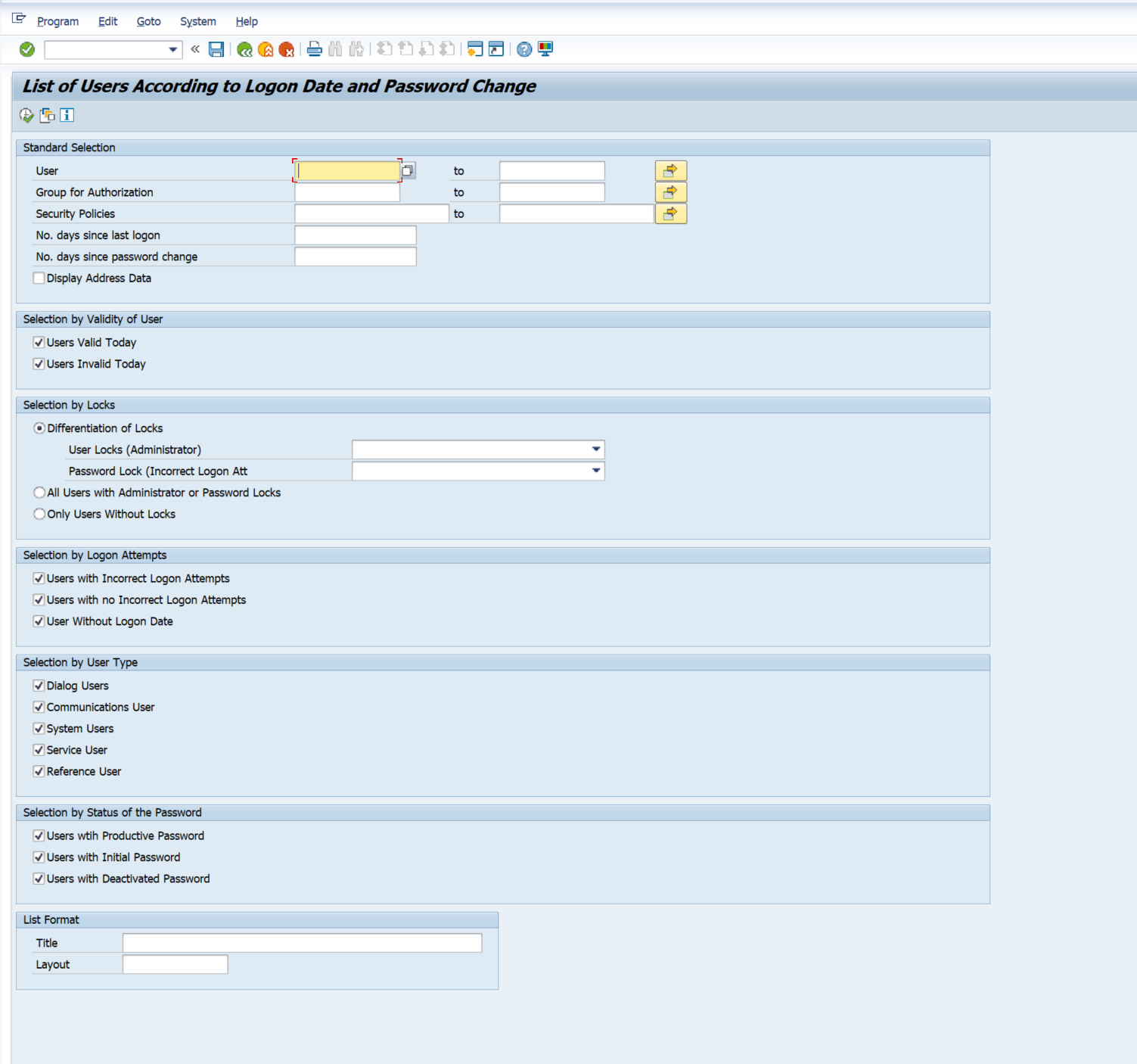
Navigate to this data by using the RSUSR200 transaction code. Then enter the desired selection parameters and the Execute button.
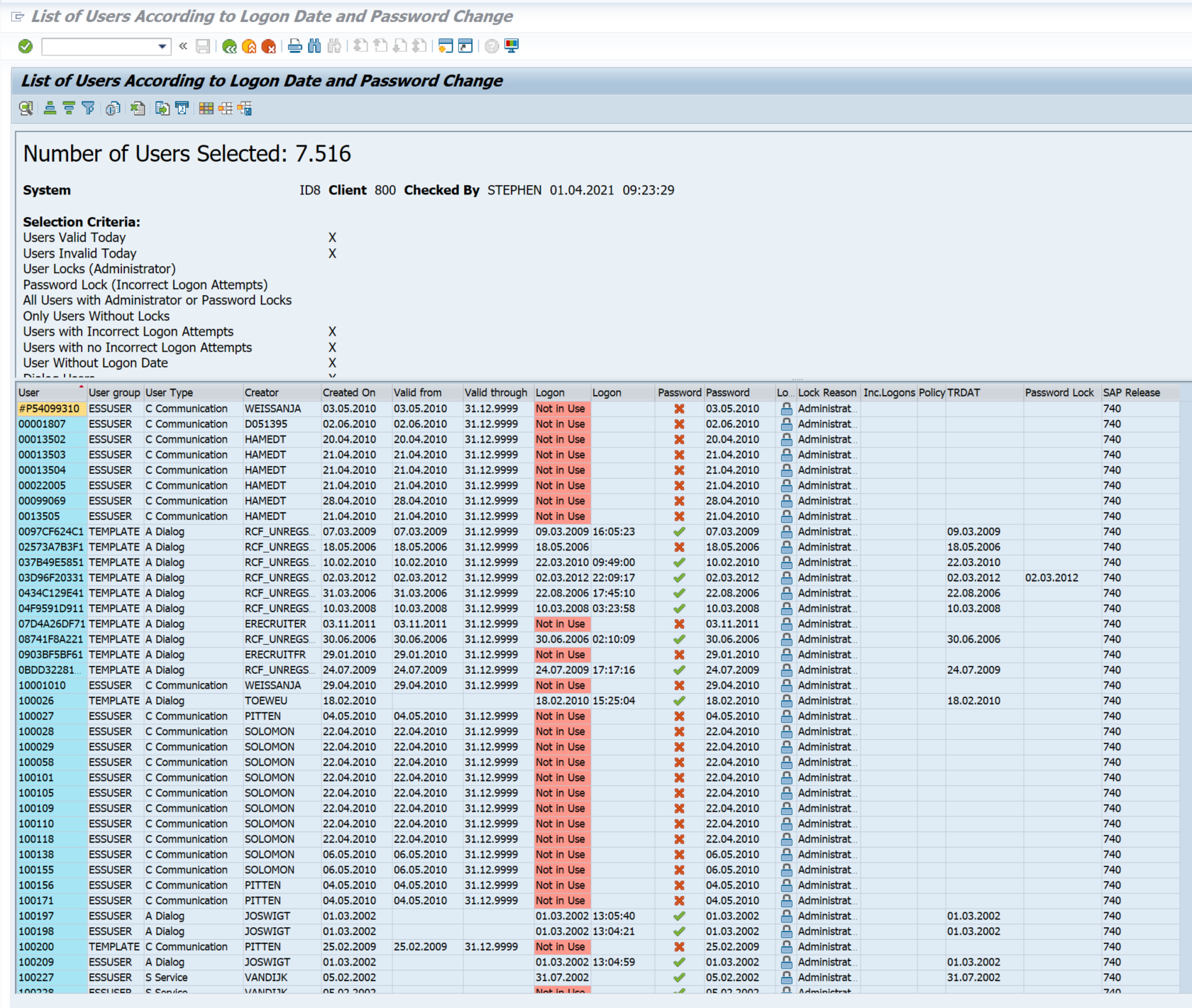
The data displayed below will match with what you see in Splunk.