Data Description
The SM20 event is used in SAP to view the security audit log.
Potential Use Cases
This event could be used in the following scenarios:
-
Dashboard audit log messages to view messages by criticality
-
Alert on specific audit log messages
-
Correlate the data from the system audit log with other data points such as user log-ins and authorization objects to identify potential malicious behavior.
Metric Filters
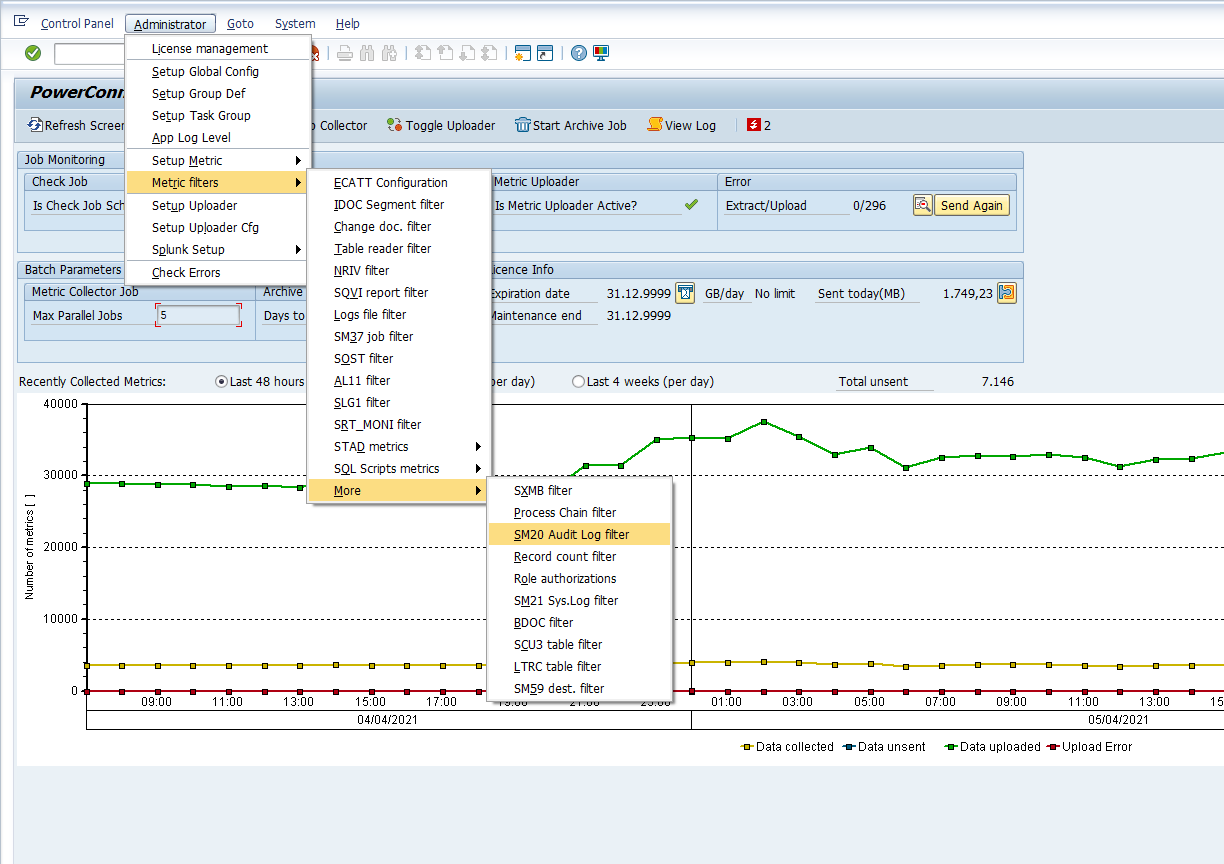
This filter is used to select or exclude specific messages from the audit log and is an optional configuration to control data volume sent to Splunk. To access the metric filter log into the managed system and execute the /n/bnwvs/main transaction. Then go to Administrator → Metric Filters → More → SM20 Audit log filter.
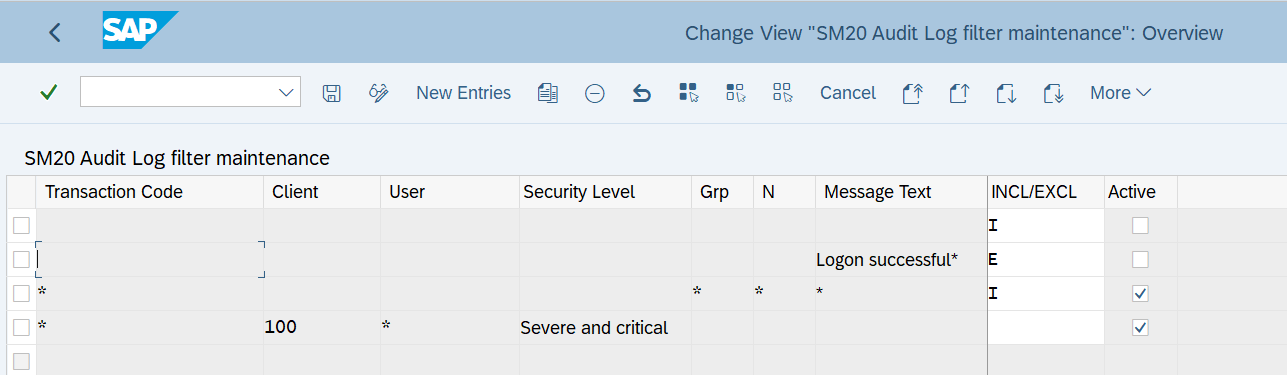
Then select the New Entries button, and enter the user selection parameters using the fields below, and save the configuration:
-
Transaction Code - This field is mandatory and is used to filter on a specific transaction code that is noted within the security audit log. To extract data from all transactions, enter a wildcard value (i.e. “*”).
-
Client - This field is mandatory and is used to filter on a specific client of the SAP system that is noted within the security audit log. To extract data from all the clients, enter a wildcard value (i.e. “*”).
-
User - This field is mandatory and is used to filter on a specific user that is noted within the security audit log. To extract data for all the users, enter a wildcard value (i.e. “*”).
-
Security Level - This field is mandatory and is used to filter on a specific 'Security Level' message that is noted within the security audit log. To extract data for all security level, enter a wildcard value (i.e. “*”).
-
Grp - This field is mandatory and represents the system log message group. To extract data for all message groups, enter a wildcard value.
-
N - This field is mandatory and represents the message group sub-name. To extract data for all the message group sub-names, enter a wildcard value.
-
Message Text - This field is mandatory and represents the message text from the system log. To extract data for all messages, enter a wildcard value.
-
INCL/EXCL - This field is mandatory and is an exclusion or inclusion criteria. To exclude the values defined in the selection criteria enter an “E“ in the field. Similarly, to include the values defined in the selection criteria enter an “I” in the field.
-
Active - This field is mandatory and is a checkbox used to enable or disable the filter criteria. To activate the filter criteria, ensure the checkbox is checked. Conversely, if you would like to disable data collection ensure the checkbox is unchecked.
Here is an example of what the filter can look like once it is filled out:
Splunk Event
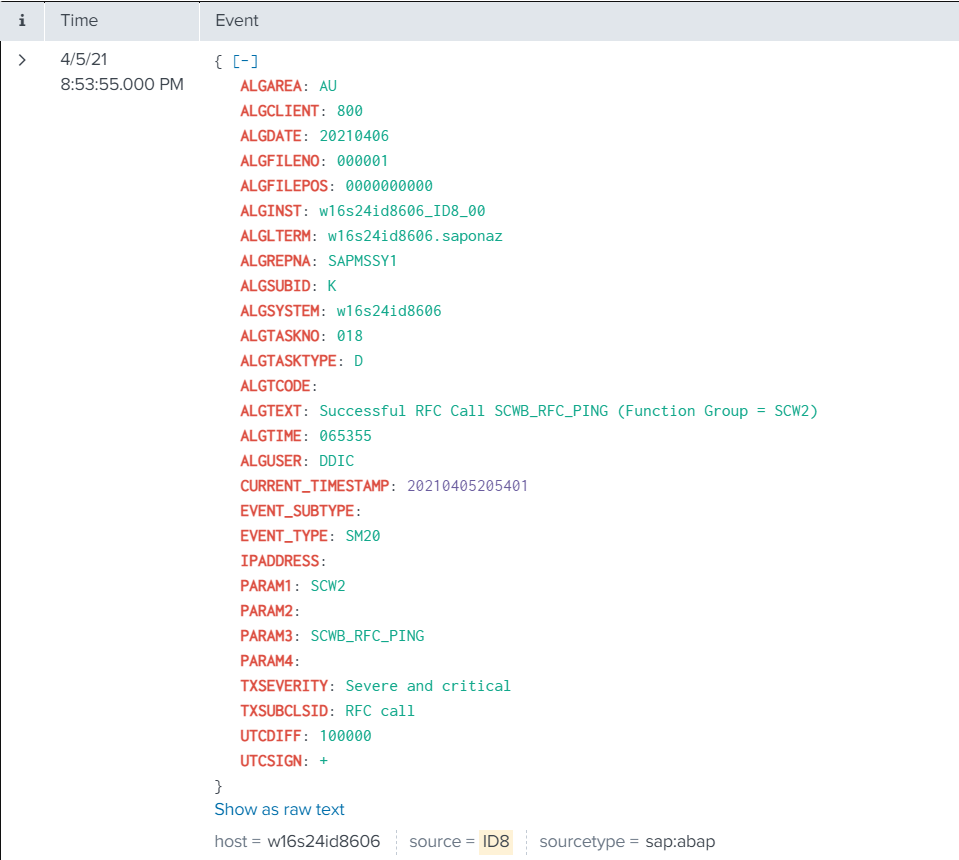
The event will look like this in Splunk:
SAP Navigation
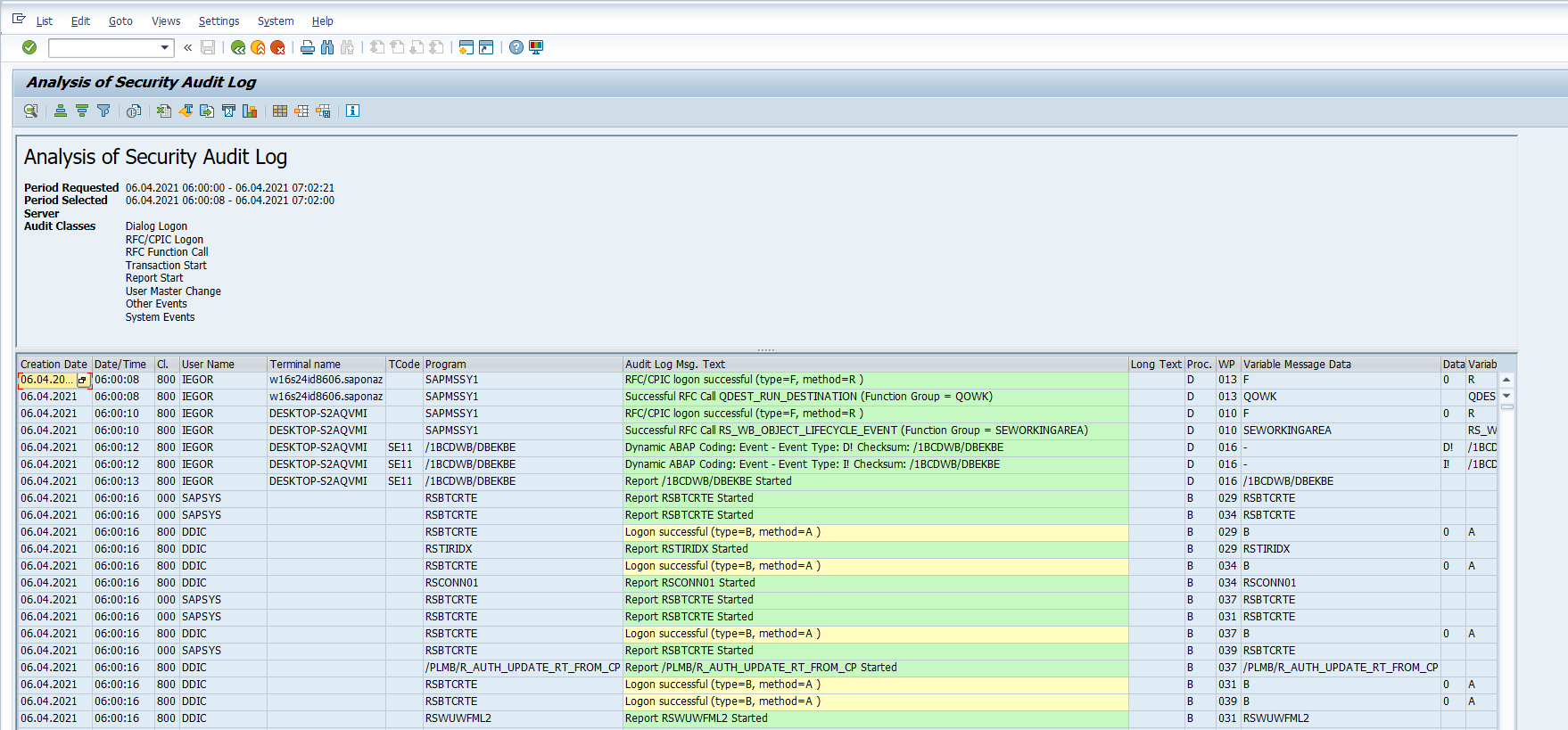
Log into the managed system and execute the SM20 transaction. Then fill in the desired user selection parameters and hit the Reread Audit Log.
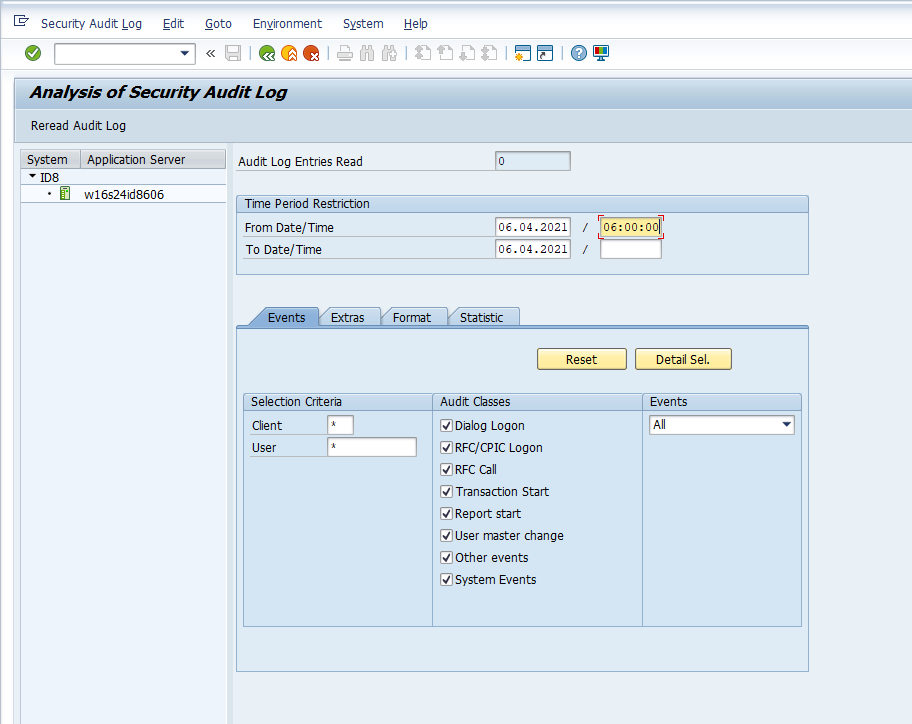
The data displayed will match the data collected and sent to Splunk.